STOP HUNTING, START VERIFYING
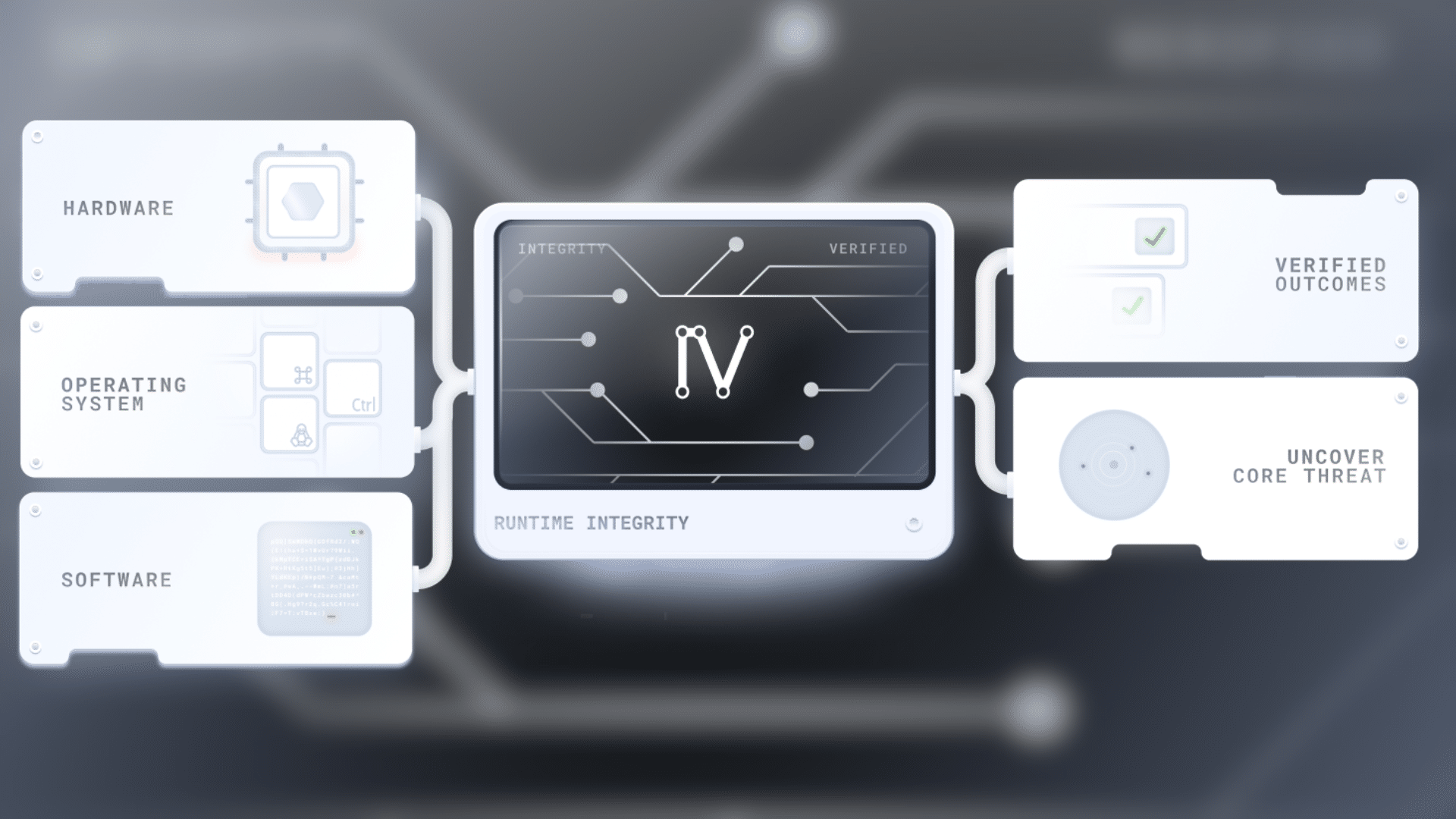
Most cybersecurity companies hunt for threats. They scan for signatures, chase anomalies and race to identify the next threat before it spreads. Invary was founded on a different approach: instead of chasing every new threat, it defines exactly how a system is supposed to behave and continuously verifies it.
“Bad guys have a lot of tools, and they’re able to create malware that’s really novel and specific to the machines that they’re attacking that nobody’s seen before,” said Jason Rogers, CEO of Invary. “We feel this is actually the only way forward for cybersecurity. As opposed to looking for the bad thing, we’re making sure we’re only doing the good things.”
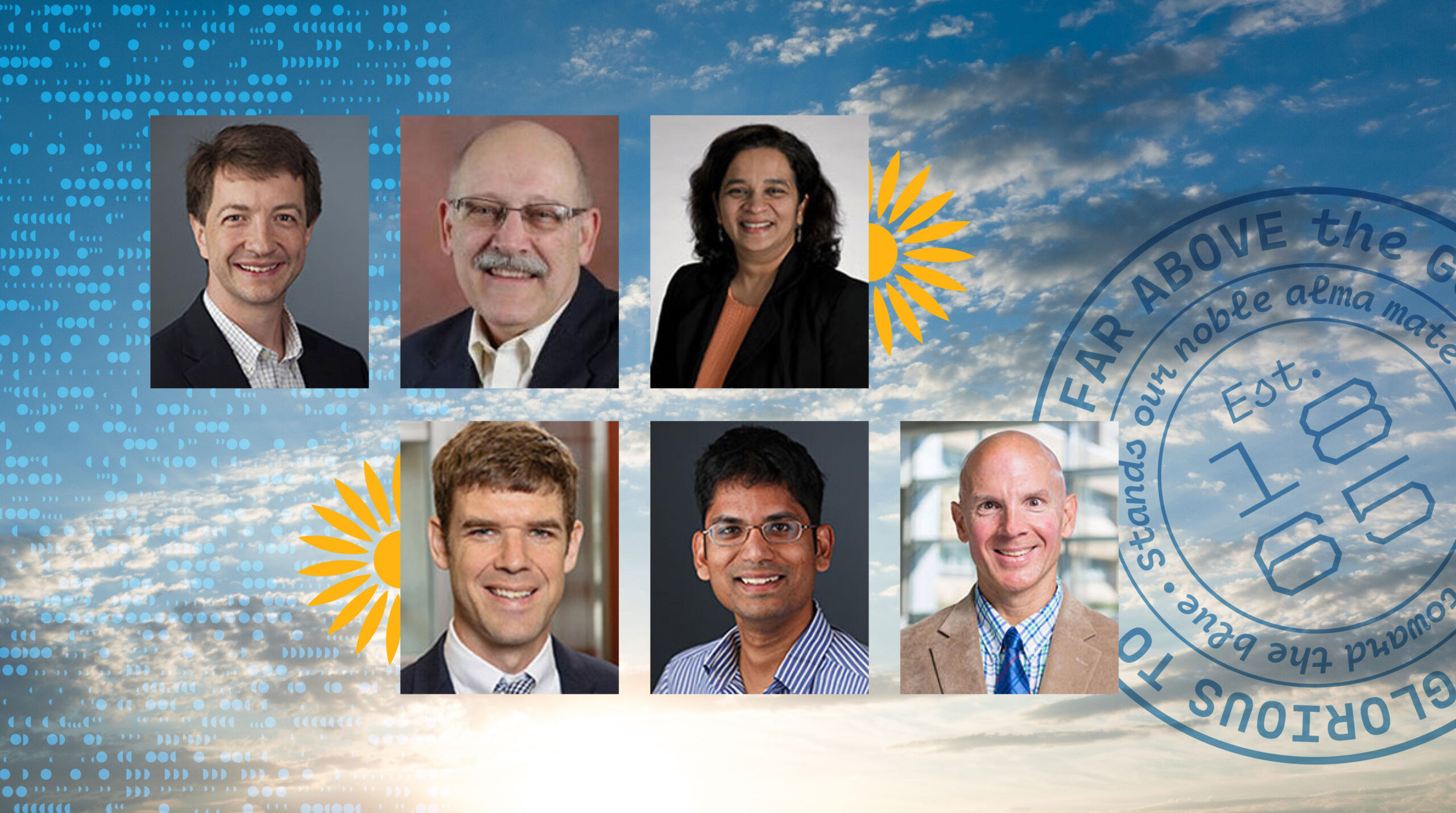
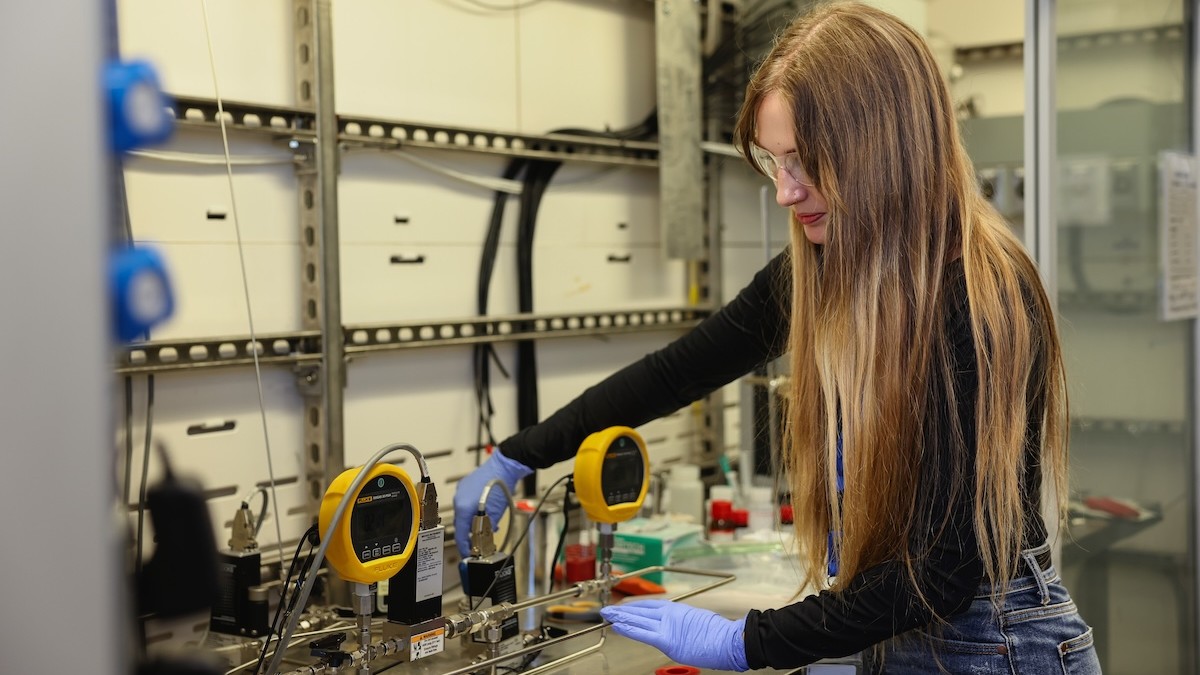
FROM RESEARCH TO RUNTIME
Dr. Wesley Peck is well-versed in the technology powering Invary, considering it was part of his dissertation work at the University of Kansas with Dr. Perry Alexander, AT&T Foundation Distinguished Professor of Electrical Engineering and Computer Science.
This leading-edge technology was once kept behind classified doors. “The NSA developed this technology and used it internally for a while,” Peck said. Employees went to the director of the agency to share the impact the technology could have on the cybersecurity industry, suggesting it go beyond government use. Invary has an exclusive license, as well as an ongoing research relationship with the NSA. The commercialized result is Runtime Integrity, which is focused on verifying the security and confidentiality of systems and is available to both the public and private sectors.
Rogers says an easy way to describe how Invary’s technology works is to imagine trying to find a needle in a haystack. “Most cybersecurity companies are looking for that needle in the haystack,” he said. Maybe they’re focused on finding a bad piece of software or how it got there, which can be disruptive. “We measure the haystack so we know how much it weighs, how tall it is,” Rogers explained. “If it’s an ounce bigger or an inch taller, we know there’s a needle in there. And in fact, because of how we measure the haystack, we can say exactly where the needle is.”
Invary’s Runtime Integrity doesn’t need to be familiar with a threat to detect compromise. Instead, it verifies systems in a known-good state, exposing novel attacks without relying on prior indicators. “We’re focused on zero days, things other people can’t find, and these pieces of malware, they can embed themselves in the system and confuse the rest of the security stack,” Rogers said.
RISK IS UNIVERSAL
Sophisticated attacks are no longer reserved for only large or high-value targets. “These threat actors are as automated and as advanced as any technology company in the U.S., and they’re attacking everybody and their tools don’t discriminate,” Peck said.
Rogers said the volume of attacks, their rate of change, and their novelty are among the things that worry him as a cybersecurity professional, especially when it comes to critical infrastructure. But on the flip side, there are many meaningful developments on the defensive side, too. “We get a chance to work with the best and brightest in the government and in industry. There’s a lot of collaboration going on,” he said. “Part of Invary’s mission is to protect all of that, from the most sensitive systems at the NSA down to the single accountant who lives in Utah. We want to make sure everyone has the same protection.”
PERKS OF THE PARK
KU Innovation Park has supported Invary from the research lab to the market, helping to form the company and supporting its back-office operations. “KU Innovation Park has been an excellent partner,” Rogers said. “We make use of the facilities here, which gives us a place to collaborate.”
That early assistance also allowed the Invary team to focus on their mission and begin raising capital. So far, Invary has done an angel round, a pre-seed round, and most recently, a $3.5 million seed round, putting the company on a true venture trajectory. And their customer base runs the gamut. “We serve the NSA, the Department of the Navy. We have work going on at the CIA, so some of our most critical systems,” Rogers said. “It’s equally valuable to go help that single tax accountant or the small mom-and-pop shop, and all the enterprises and SMB businesses in between.”